This is the second and final part of the 2-series interview where Dr. Garima Gupta and Dr. Gaurav Gupta talk about safety tips related to PC.
You can read the part 1 of this interview: [Interview] Top Cyber Experts on keeping your smartphone safe
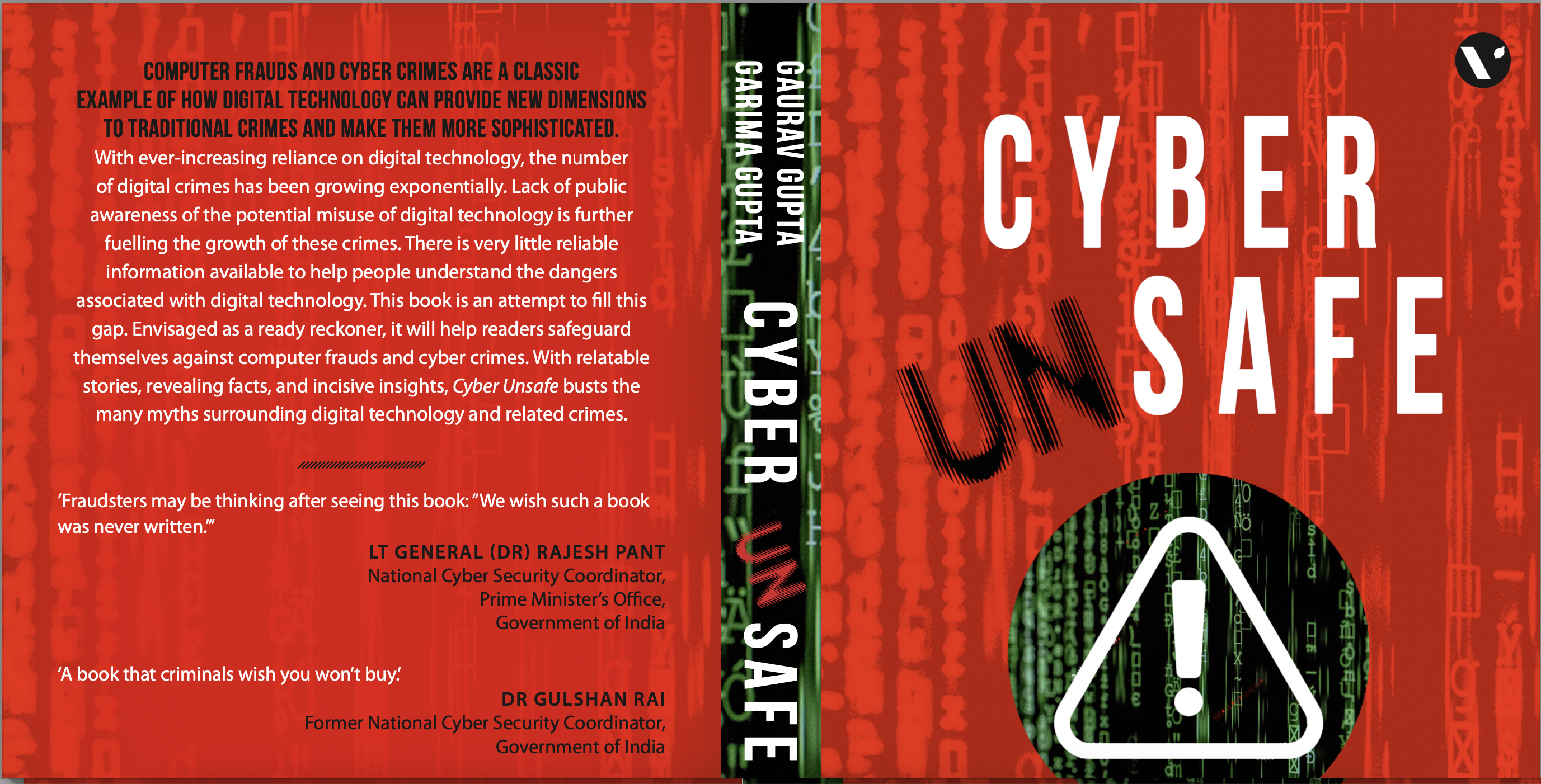
Dr. Garima Gupta and Dr. Gaurav Gupta are authors of “Cyber Unsafe” – a book that has tried to analyze computer fraud and cybercrime issues from a common man’s perspective and unmasks the myths associated with the subjects. They have used relatable real-world incidents and stories to demonstrate the risks of digital technology. Further, easy-to-implement, mostly non-technical, methods have been identified for technology users to help them safeguard against prevailing computer frauds and cybercrimes.
The book is available on Amazon.


In this part of the interview, Dr. Garima Gupta and Dr. Gaurav Gupta talk about safety tips specific to PC.
How do we know if an email is genuine or a scam?
Spelling mistakes, unsolicited offers, and promises too good to be true, then there is a high chance that the email is fraudulent. Fraudulent emails also contain an attachment with catchy names. Never download and open these attachments.
How do you define a strong password? What is an ideal password policy?
The best method of creating a strong password (soon, passwordless solutions will emerge leveraging next-generation biometrics and quantum computing) is to use the initial letters of a phrase that is easy to remember. For example, the term could be ‘I love my two sons, Dhruv and Aditya’; the password for Flipkart could be ‘Ilmy2s@D&A@flip’.
In this way, you may use the exact phrase for different sites by changing the last four letters depending on the site’s name. We can create a 15-character strong password adhering to all the password rules with this technique.
With the rise of connected devices such as IoT, it’s easy for users to be tracked and, in worst cases, even spied on by hackers. How do you suggest people should deal with such devices and services?
Read about how data from IoT is compromised, including side-channel attacks. Always switch on encryption and other security features and avoid using these devices in sensitive cases as they leak information.
Where do you stand when it comes to cloud hosting vs. NAS hosting for regular users? Why? Which cloud service would you recommend?
It depends on your requirement, i.e., the cloud helps you avoid Capex, and NAS requires Capex and one needs to spend on security, maintenance, and operations. You need to protect your data in the cloud, and the preferred way is to use encryption. The choice of a service provider is typically dependent on the economics of the service.
Is antivirus still important? If so, shall users of Non-Windows machines such as macOS and ChromeOS be using Antivirus software?
If you follow safe browsing practices and do not use USB and other storage media on your devices, including computers and laptops, you are most likely safe. However, having an antivirus will help you further from known viruses.
What will be the top three tips by you when it comes to cyber security for everybody?
Use strong passwords. Learn from other mistakes and read about prevailing cyber security incidents and cybercrime modus operandi. One such resource is the book “Cyber Unsafe” by Gaurav Gupta and Garima Gupta, available on Amazon.
Are we supposed to be using VPN?
It’s unnecessary to use VPN, and VPN is typically used to visit sites blocklisted through the firewall in an organization/ network/ country.
How do I make my WiFi router secure?
The first is to change the default password and keep changing passwords often. Also, switch off the router when not in use.
